https://www.europesays.com/1961251/ EJÉRCITO ESPAÑOL | ¿A quiénes reclutarían primero si España entrara en guerra? #ciudadanos #Constitución #dv #Ejército #España #Guerra #llamarian #noticias #quien #recluta #sociedad #soldados #spain
Viimatised otsingud
Otsimisvalikud
#dv
@emu : given a domain name (*) for a website with an APPARENT owner, DV certs do not provide ANY security because users have no reasonable way to determine whether said domain name DOES NOT belong to the apparent owner.
Phishing is wreaking havoc on the internet. There are lots of people like you who DO NOT provide ANY solutions.
(*) In some message (email, SMS, chatapp, DM, ...), found by Googling, out of a QR-code, in a paper letter or on social media.
A DV cert may be fine for your home NAS, but not for your bank. Unfortunately big tech does not want users to see the difference between a fake and a real bank (or any other critical website) in their browsers.
@aral :
I don't want to pay a cent. Neither donate, nor via taxes.

@aral : most Let's Encrypt (and other Domain Validated) certificates are issued to junk- or plain criminal websites.
They're the ultimate manifestation of evil big tech.
They were introduced to encrypt the "last mile" because Internet Service Providers were replacing ads in webpages and, in the other direction, inserting fake clicks.
DV has destroyed the internet. People loose their ebank savings and companies get ransomwared; phishing is dead simple. EDIW/EUDIW will become an identity fraud disaster (because of AitM phishing atracks).
Even the name "Let's Encrypt" is wrong for a CSP: nobody needs a certificate to encrypt a connection. The primary purpose of a certificate is AUTHENTICATION (of the owner of the private key, in this case the website).
However, for human beings, just a domain name simply does not provide reliable identification information. It renders impersonation a peace of cake.
Decent online authentication is HARD. Get used to it instead of denying it.
REASONS/EXAMPLES
Troy Hunt fell in the DV trap: https://infosec.exchange/@ErikvanStraten/114222237036021070
Google (and Troy Hunt!) killed non-DV certs (for profit) because of the stripe.com PoC. Now Chrome does not give you any more info than what Google argumented: https://infosec.exchange/@ErikvanStraten/114224682101772569
https:⧸⧸cancel-google.com/captcha was live yesterday: https://infosec.exchange/@ErikvanStraten/114224264440704546
Stop phishing proposal: https://infosec.exchange/@ErikvanStraten/113079966331873386
Lots of reasons why LE sucks:
https://infosec.exchange/@ErikvanStraten/112914047006977222 (corrected link 09:20 UTC)
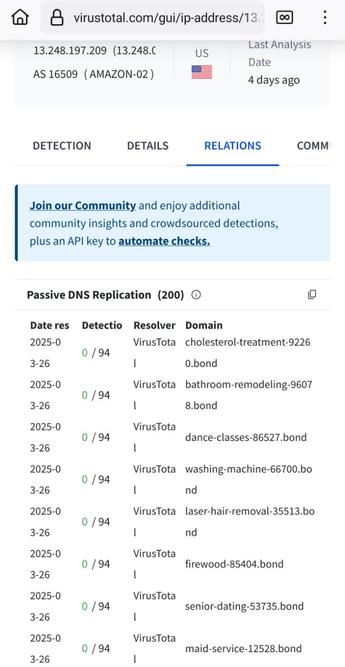
This website stopped registering junk .bond domain names, probably because there were too many every day (the last page I found): https://newly-registered-domains.abtdomain.com/2024-08-15-bond-newly-registered-domains-part-1/. However, this gang is still active, open the RELATIONS tab in https://www.virustotal.com/gui/ip-address/13.248.197.209/relations. You have to multiply the number of LE certs by approx. 5 because they also register subdomains and don't use wildcard certs. Source: https://www.bleepingcomputer.com/news/security/revolver-rabbit-gang-registers-500-000-domains-for-malware-campaigns/
@troyhunt : if we open a website that we've never visited before, we need browsers to show us all available details about that website, and warn us if such details are not available.
We also need better (readable) certificates identifying the responsible / accountable party for a website.
We have been lied to that anonymous DV certificates are a good idea *also* for websites we need to trust. It's a hoax.
Important: certificates never directly warrant the trustworthyness of a website. They're about authenticity, which includes knowing who the owner is and in which country they are located. This helps ensuring that you can sue them (or not, if in e.g. Russia) which *indirectly* makes better identifiable websites more reliable.
More info in https://infosec.exchange/@ErikvanStraten/113079966331873386 (see also https://crt.sh/?Identity=mailchimp-sso.com).
Note: most people do not understand certificates, like @BjornW in https://mastodon.social/@BjornW/114064065891034415:
❝
@letsencrypt offers certificates to encrypt the traffic between a website & your browser.
❞
2x wrong.
A TLS v1.3 connection is encrypted before the website sends their certificate, which is used only for *authentication* of the website (using a digital signature over unguessable secret TLS connection parameters). A cert binds the domain name to a public key, and the website proves possession of the associated private key.
However, for people a domain name simply does not suffice for reliable identification. People need more info in the certificate and it should be shown to them when it changes.
Will you please help me get this topic seriously on the public agenda?
Edited 09:15 UTC to add: tap "Alt" in the images for details.
@0xF21D : Cloudflare is evil anyway.
Cloudflare reverse-proxies (or -proxied):
-
cloudflare.com.save-israel·org
-
ns.cloudflare.com.save-israel·org
-
albert.ns.cloudflare.com.save-israel·org
-
sydney.ns.cloudflare.com.save-israel·org
-
I don't know whether any of these domains were or are malicious, but such domain names are insane; expect evilness.
See also:
https://crt.sh/?Identity=save-israel.org
Tap "Alt" in the images for more info.
https://www.europesays.com/1919749/ Llega a España el ‘boomerasking’: el fenómeno ligado a la necesidad de atención que preocupa a los psicólogos #boomerasking #dv #Ego #egoistas #Emociones #España #noticias #preguntas #psicología #spain
https://www.europesays.com/1914438/ VIDEO CUBANA ESPAÑA | Una cubana viviendo en España explica las diferencias con su país: “No se puede hacer ruido” #agua #Cuba #cubana #culturales #diferencias #dv #España #explica #Galicia #noticias #spain #TikTok #turismo #viviendo


![Screenshot of https://www.virustotal.com/gui/domain/mailchimp-sso.com/relations
It shows that mailchimp-sso[.]com is "hosted" (actally proxied) by Cloudflare IP-addresses. Screenshot of https://www.virustotal.com/gui/domain/mailchimp-sso.com/relations
It shows that mailchimp-sso[.]com is "hosted" (actally proxied) by Cloudflare IP-addresses.](https://est.social/system/cache/media_attachments/files/114/222/237/157/347/946/small/a96c1d8a9e7a2fab.jpeg)
![Screenshot of https://www.virustotal.com/gui/domain/mailchimp-sso.com/details
It shows that mailchimp-sso[.]com has a DV-certificate issued by "Google Trust Services". Screenshot of https://www.virustotal.com/gui/domain/mailchimp-sso.com/details
It shows that mailchimp-sso[.]com has a DV-certificate issued by "Google Trust Services".](https://est.social/system/cache/media_attachments/files/114/222/237/168/539/178/small/2dc2489dfdb36fa2.jpeg)
![Screenshot from part of https://www.virustotal.com/gui/ip-address/188.114.96.0/relations
Visible in the screenshot (using '-' on a line on itself as line separator, and replaced the last dot in domain names by "[.]" to prevent accidental opening):
-
2025-03-17 0/94 Mandiant albert.ns.cloudflare.com.save-israel.org
-
2025-03-17 19/94 Mandiant allegro.pl-oferta5260043.shop
-
2025-03-17 19/94 Mandiant allegro.pl-ogloszenia78517.shop
-
2025-03-17 6/94 Mandiant allegrolokalnie.8124-4912-9124.rest
-
2025-03-17 17/94 Mandiant allegrolokalnie.d9llje3ubkij00gv.shop
-
2025-03-17 21/94 Mandiant allegrolokalnie.oferta-3156512.shop
-
2025-03-17 19/94 Mandiant allegrolokalnie.oferta-8681986.sbs
-
2025-03-17 19/94 Mandiant allegrolokalnie.ogloszenie-9908905.shop
- Screenshot from part of https://www.virustotal.com/gui/ip-address/188.114.96.0/relations
Visible in the screenshot (using '-' on a line on itself as line separator, and replaced the last dot in domain names by "[.]" to prevent accidental opening):
-
2025-03-17 0/94 Mandiant albert.ns.cloudflare.com.save-israel.org
-
2025-03-17 19/94 Mandiant allegro.pl-oferta5260043.shop
-
2025-03-17 19/94 Mandiant allegro.pl-ogloszenia78517.shop
-
2025-03-17 6/94 Mandiant allegrolokalnie.8124-4912-9124.rest
-
2025-03-17 17/94 Mandiant allegrolokalnie.d9llje3ubkij00gv.shop
-
2025-03-17 21/94 Mandiant allegrolokalnie.oferta-3156512.shop
-
2025-03-17 19/94 Mandiant allegrolokalnie.oferta-8681986.sbs
-
2025-03-17 19/94 Mandiant allegrolokalnie.ogloszenie-9908905.shop
-](https://est.social/system/cache/media_attachments/files/114/187/494/628/951/049/small/9fc8bf05357a0271.jpeg)
![Screenshot from part of https://www.virustotal.com/gui/domain/cloudflare.com.save-israel.org/relations
Visible in the screenshot (using '-' on a line on itself as line separator, and replaced the last dot in domain names by "[.]" to prevent accidental opening):
-
Passive DNS Replication (2)
-
Date resolved Detections Resolver IP
-
2024-07-31 0/94 VirusTotal 172.67.169.79
-
2024-07-31 0/94 VirusTotal 104.21.87.91
-
Subdomains (1)
-
ns.cloudflare.com.save-israel.org 0/94 172.67.169.79 104.21.87.91
-
Siblings (2)
-
com.save-israel.org 0/94 172.67.169.79 104.21.87.91
-
www.save-israel.org 0/94 63.250.43.12 63.250.43.11
- Screenshot from part of https://www.virustotal.com/gui/domain/cloudflare.com.save-israel.org/relations
Visible in the screenshot (using '-' on a line on itself as line separator, and replaced the last dot in domain names by "[.]" to prevent accidental opening):
-
Passive DNS Replication (2)
-
Date resolved Detections Resolver IP
-
2024-07-31 0/94 VirusTotal 172.67.169.79
-
2024-07-31 0/94 VirusTotal 104.21.87.91
-
Subdomains (1)
-
ns.cloudflare.com.save-israel.org 0/94 172.67.169.79 104.21.87.91
-
Siblings (2)
-
com.save-israel.org 0/94 172.67.169.79 104.21.87.91
-
www.save-israel.org 0/94 63.250.43.12 63.250.43.11
-](https://est.social/system/cache/media_attachments/files/114/187/494/640/993/577/small/927600ba502354c2.jpeg)
![Screenshot from part of https://www.virustotal.com/gui/domain/ns.cloudflare.com.save-israel.org/relations
A bit more text than visible in the screenshot (using '-' on a line on itself as line separator, and replaced the last dot in domain names by "[.]" to prevent accidental opening):
-
Passive DNS Replication (2)
-
Date resolved | Detections | Resolver | IP
-
2024-07-31 | 0/94 | VirusTotal | 172.67.169.79
-
2024-07-31 | 0/94 | VirusTotal | 104.21.87.91
-
Subdomains (2)
-
albert.ns.cloudflare.com.save-israel[.]org 0/ 94 188.114.96.0 188.114.97.0 188.114.96.9 ...
-
sydney.ns.cloudflare.com.save-israel[.]org
0/94 188.114.96.0 188.114.97.0 188.114.96.9 ...
-
Siblings (2)
-
com.save-israel[.]org 0/94 172.67.169.79 104.21.87.91
-
www.save-israel[.]org 0/94 63.250.43.12 63.250.43.11
- Screenshot from part of https://www.virustotal.com/gui/domain/ns.cloudflare.com.save-israel.org/relations
A bit more text than visible in the screenshot (using '-' on a line on itself as line separator, and replaced the last dot in domain names by "[.]" to prevent accidental opening):
-
Passive DNS Replication (2)
-
Date resolved | Detections | Resolver | IP
-
2024-07-31 | 0/94 | VirusTotal | 172.67.169.79
-
2024-07-31 | 0/94 | VirusTotal | 104.21.87.91
-
Subdomains (2)
-
albert.ns.cloudflare.com.save-israel[.]org 0/ 94 188.114.96.0 188.114.97.0 188.114.96.9 ...
-
sydney.ns.cloudflare.com.save-israel[.]org
0/94 188.114.96.0 188.114.97.0 188.114.96.9 ...
-
Siblings (2)
-
com.save-israel[.]org 0/94 172.67.169.79 104.21.87.91
-
www.save-israel[.]org 0/94 63.250.43.12 63.250.43.11
-](https://est.social/system/cache/media_attachments/files/114/187/494/653/873/067/small/b5210dd29b8048ca.jpeg)

